In this 3-part series we are demonstrating how nGuard most commonly gains an initial foothold on internal networks, then takes that initial access and pivots through the network to obtain full command and control over systems. If you missed part I, check it out here.
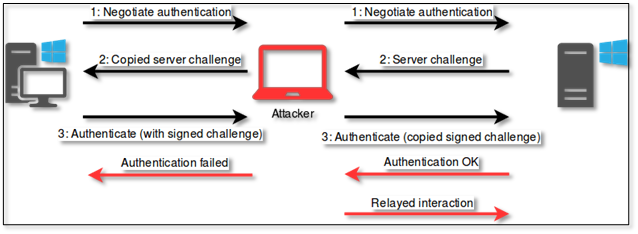
In this second part, we are going to take the hashes we have intercepted from part I and build upon it. We are going to relay the hashes to other hosts on the network and see what permissions and access we have. This attack is different than another common attack called pass-the-hash (PTH). Since the hashes we have captured with our Responder tool are Net-NTLM hashes, we cannot perform the PTH attack. Instead, we relay them to discover local NTLM hashes, which we can perform the PTH attack with.
In this attack we are going to use CrackMapExec and Impacket’s ntlmrelayx Python module. CrackMapExec is a post-exploitation tool that is used in assessing Active Directory environments. This is a tool with many features, but we will only be showing the feature of generating a list with hosts that have Server Message Block (SMB) Singing disabled/not required. To do this we run the command:
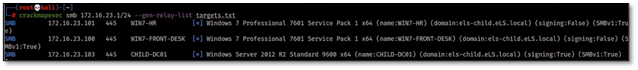
crackmapexec smb <IP Range to scan> –gen-relay-list <outputFileName.txt>
This command specifies the name of the tool, the protocol we want to scan for (SMB), command to generate a list, and the name of the file where we want to output the hosts with SMB signing disabled. In the screenshot below you can see we discover two hosts with SMB singing as false (disabled).
The Impacket module ntlmrelayx.py allows us to take the Net-NTLM hashes we captured in Responder and perform SMB relay attacks on the hosts discovered with SMB signing disabled utilizing CrackMapExec. The default behavior of this module is to dump the local Security Account Manager (SAM) file which contains local NTLM hashes. These are hashes we can now perform the PTH with. The two screenshots below demonstrate how this attack is carried out.
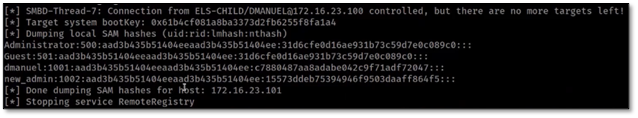
As we obtain these hashes throughout these attacks, we will always upload them into our password cracking machine and attempt to discover the cleartext password. As demonstrated in these videos so far, there are many things we can do with hashes, but working with the cleartext is always easier.
Here is a video demonstrating this in action:
In part 3 we will take the access we have gained, use that to setup full command and control over a specific host, and view the results of the hashes being uploaded into our password cracker. If you have any questions about this attack or want to see if nGuard can perform attacks like this on your internal network during one of our internal penetration testing assessments please reach out to an Account Executive.


